Enterprise security costs $50, 000/year. A Sophos XGS firewall starts at $1, 500. CrowdStrike charges $8.99/endpoint/month. For small businesses, home labs, and the 90% of the world that can't afford this — there's nothing.
Meanwhile, attackers collaborate in forums and marketplaces. They share tools, exploits, and zero-days freely. Defenders fight alone, behind expensive black boxes they can't audit, running algorithms they can't understand, sending their data to clouds they don't control.
I decided to change that.
What I BuiltHookProbe is an **AI-native intrusion detection system** that runs entirely on a **Raspberry Pi 5** (8GB RAM, $75). It processes network traffic at the kernel level using eBPF/XDP, classifies threats with machine learning, and defends autonomously — no human intervention required.
In the last 42 days of production operation, this single Raspberry Pi:
- Processed **8.8 million security events**
- Classified **177, 000 ML verdicts** (45% benign, 40% malicious, 13% suspicious)
- Tracked **11, 832 unique attacker IP addresses**
- Discovered **3, 845 Indicators of Compromise**
- Detected **1, 120 attack patterns** using temporal and sequential analysis
- Maintained a security posture score of **73/100 (GREEN — Protected)**
All of this running on ARM silicon. No cloud. No subscription. No data ever leaves the edge.
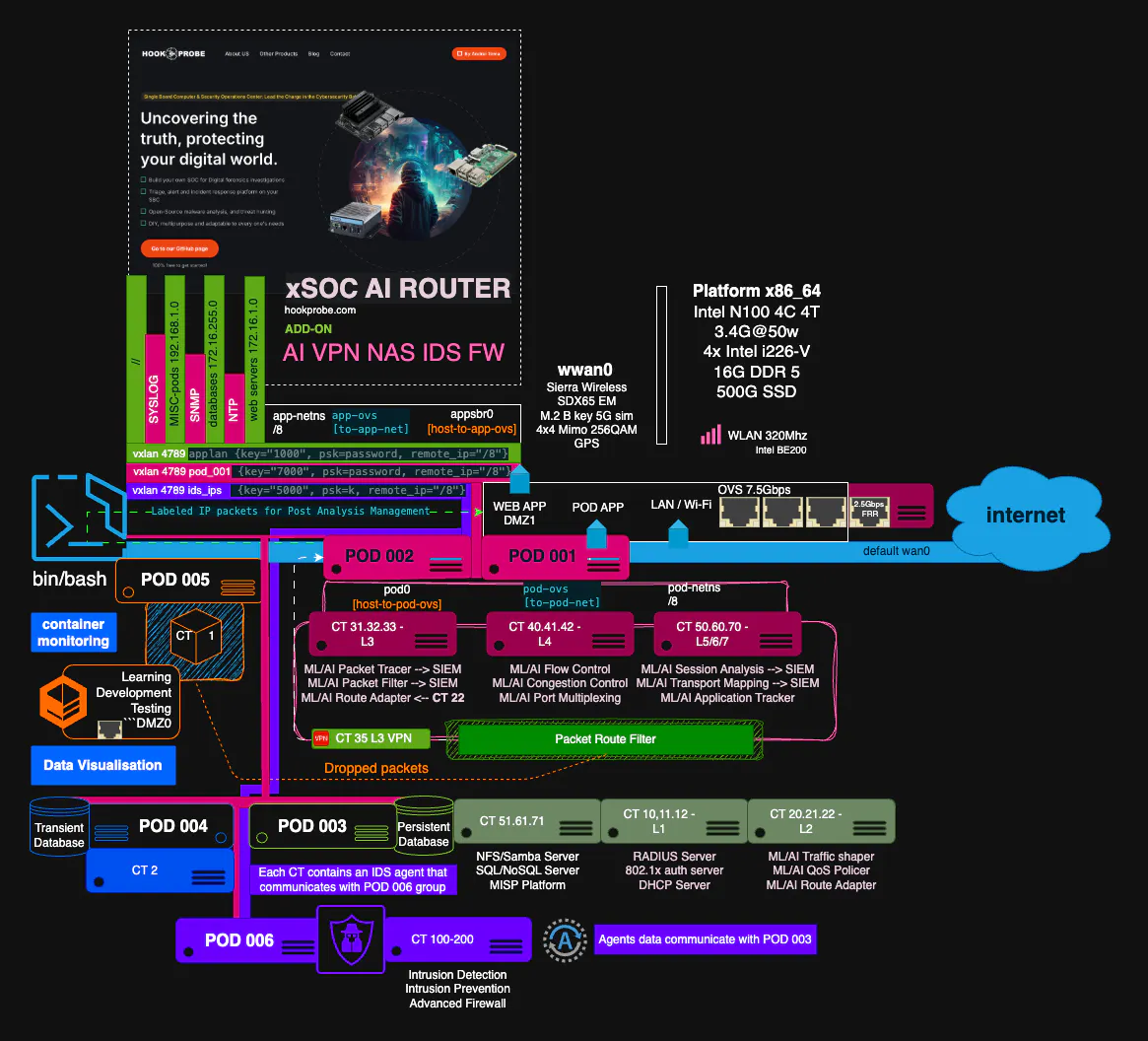
The ArchitectureHookProbe is not a single tool — it's a complete security stack:
**NAPSE** (Neural Adaptive Packet Synthesis Engine) — AI-native IDS that performs L2-L7 deep packet inspection. Unlike Suricata or Snort which rely on signature matching, NAPSE classifies traffic using ML models that learn what "normal" looks like for your network.
**HYDRA** (Threat Intelligence Pipeline) — Syncs with Spamhaus DROP, FireHOL, and other threat feeds. Enriches every IP with RDAP/WHOIS data, anomaly scores, and behavioral features. Feeds the ML pipeline with real-time intelligence.
**SENTINEL** (ML Classification Engine) — A Bayesian ensemble that classifies every source IP as benign, suspicious, or malicious. Trained on real production data with isotonic calibration for accurate probability estimates.
**AEGIS** (Autonomous Defense) — 8 specialized AI agents that orchestrate response: triage, investigate, contain, remediate, learn. No human in the loop for routine threats.
**XDP/eBPF** (Kernel-Level Filtering) — Custom C programs loaded into the Linux kernel's XDP hook. Packets are classified at wire speed before they ever reach userspace. DDoS mitigation, rate limiting, and blocklist enforcement happen in nanoseconds.
**CNO** (Cognitive Network Organism) — The newest layer: a brainstem/cerebellum/cerebrum architecture that gives the system "fight or flight" responses. When stress is high, it prioritizes vital traffic and defers non-critical flows.
```
┌─────────────────────────────────────────┐
│ HOOKPROBE STACK │
├─────────────────────────────────────────┤
│ XDP/eBPF → Kernel packet filtering │
│ NAPSE → AI packet classification │
│ HYDRA → Threat intelligence │
│ SENTINEL → ML verdict engine │
│ AEGIS → Autonomous defense │
│ CNO → Cognitive organism │
│ HTP/NSE → Post-quantum transport │
│ QSecBit → Security posture score │
└─────────────────────────────────────────┘
```
HardwareThe beauty of HookProbe is the hardware simplicity:
**Bill of Materials:**
| Component | Price |
|-----------|-------|
| Raspberry Pi 5 (8GB RAM) | $75 |
| 32GB microSD card (Class 10) | $8 |
| USB-C power supply (27W) | $12 |
| Ethernet cable (Cat6) | $3 |
| Case with fan (optional) | $10 |
| **Total** | **$108** |
That's it. No special hardware. No TPM. No GPU. The ML models are quantized and optimized for ARM — they run inference on the CPU.
For comparison, the cheapest commercial IDS appliance (Suricata on a Protectli vault) starts at $300+ without software licensing.
How It Works**Network Setup:**
HookProbe sits between your router and your network, or on a mirror/span port:
```
Internet → Router → [Mirror Port]
↓
Raspberry Pi 5
(HookProbe)
↓
Inspects all traffic
Blocks threats at XDP layer
Classifies with ML
Reports to dashboard
```
**Installation:**
```bash
# Clone and install — that's it
git clone https://github.com/hookprobe/hookprobe.git
cd hookprobe
sudo./install.sh --tier guardian
# Time to protection: ~5 minutes
# Ongoing maintenance: automatic
# Software cost: $0
```
The install script handles everything: packages, Python dependencies, network configuration, systemd services, XDP program loading, feed synchronization, and ML model initialization.
Production ResultsI've been running HookProbe on my home/office network for 42 days. Here's what the data shows:
**Threat Breakdown:**
| Defense Layer | Events | Unique IPs | What It Catches |
|---------------|--------|------------|-----------------|
| Rate Limiting | 3.7M | 84 | DDoS, brute-force, scanners |
| Blocklist | 1.8M | 8, 444 | Known malicious IPs from threat feeds |
| ML Score | 1.5M | 4, 795 | Novel threats, anomalous behavior |
**ML Classification Accuracy:**
The SENTINEL engine classified 177K IP behaviors:
- **78K benign** (45%) — normal traffic, no action
- **72K malicious** (40%) — escalated to blocking/throttling
- **26K suspicious** (13%) — elevated monitoring
The ML pipeline runs continuously. It doesn't need signature updates — it learns what's normal and flags deviations.
**Top Attack Type:** SSH brute-force (1, 228 classified intents). The top attacker sent 1, 063 attempts in a 2-hour burst from a single IP. XDP rate-limited it to zero throughput.
**Security Posture:** QSecBit score has been stable at 70-76/100 (GREEN — Protected) for the entire deployment. No manual intervention was required at any point.
The Software StackWritten in 5 languages, each chosen for its strength:
| Language | LOC | Purpose |
|----------|-----|---------|
| Python | ~180K | Core engines (NAPSE, HYDRA, SENTINEL, AEGIS) |
| TypeScript | ~60K | Dashboard, visualization, APIs |
| C | ~2K | eBPF/XDP kernel programs |
| Mojo | ~1K | NAPSE Brain inference (high-performance) |
| Zig | ~1K | AEGIS XDP fast-path, HSG gateway |
The system runs as **24 containers** (15 IDS + 9 web/dashboard) orchestrated with Podman (rootless for web, root namespace for IDS with kernel access).
Three TiersHookProbe scales from home to enterprise:
| Tier | Hardware | RAM | Use Case | Cost |
|------|----------|-----|----------|------|
| **Guardian** | Raspberry Pi 5 | 8 GB | Home, prosumer, small office | $75 |
| **Fortress** | Mini PC (N100) | 16 GB | Small business, branch office | $200 |
| **Nexus** | Server | 64 GB+ | Enterprise, MSSP, datacenter | $2, 000 |
Same software. Same AI. Same protection. Just different hardware capacity.
The Collective Defense VisionThe long-term vision is a mesh where every HookProbe node protects every other node:
```
Node A (Tokyo) Detects zero-day
↓
Mesh Intelligence Validates + creates signature
↓
Node B (London) Protected in <30 seconds
Node C (New York) Protected in <30 seconds
```
What gets shared: anonymized threat signatures, attack patterns, model weight updates.
What NEVER gets shared: your raw traffic, your IP addresses, your private data.
This is collective defense that respects individual privacy. Built on the HTP protocol with post-quantum Kyber KEM encryption.
Why Open Source Matters
HookProbe is AGPL v3.0. Every line of code is auditable. Every AI decision is explainable. Every threat score shows exactly why it was assigned.
The security industry runs on black boxes. "Trust us, we're protecting you." We reject that. If you can't see how your security works, you can't trust it.
> "We don't ask you to trust us. We give you the tools to verify."
Try It
**Live demo** (no login required): https://mssp.hookprobe.com/?site=demo-site
**GitHub**: https://github.com/hookprobe/hookprobe
**Documentation**: https://docs.hookprobe.com
**Monthly threat reports**: https://hookprobe.com/blog/threat-landscape-2026-03/
**Blog** (88 articles): https://hookprobe.com/blog
What's Next
- Federated learning across the mesh (share model weights, not data)
- NPU/TPU acceleration for edge inference (Apple M4, Hailo-8, Coral)
- Video content pipeline from IDS data
- Mobile app for QSecBit monitoring
- Community benchmark leaderboard
About the Builder
I'm Andrei, building HookProbe from Romania. This started as a weekend project to secure my home network and turned into a mission: make enterprise security accessible to everyone. I believe a grandmother in rural India deserves the same protection as a bank in New York.
If you want to support the project: star the repo, try the demo, or deploy a Guardian node. Every node makes the mesh stronger.
*"In a world where attackers share everything, defenders must too."*












Comments