ESP8266 WifiPhisher
Video demo
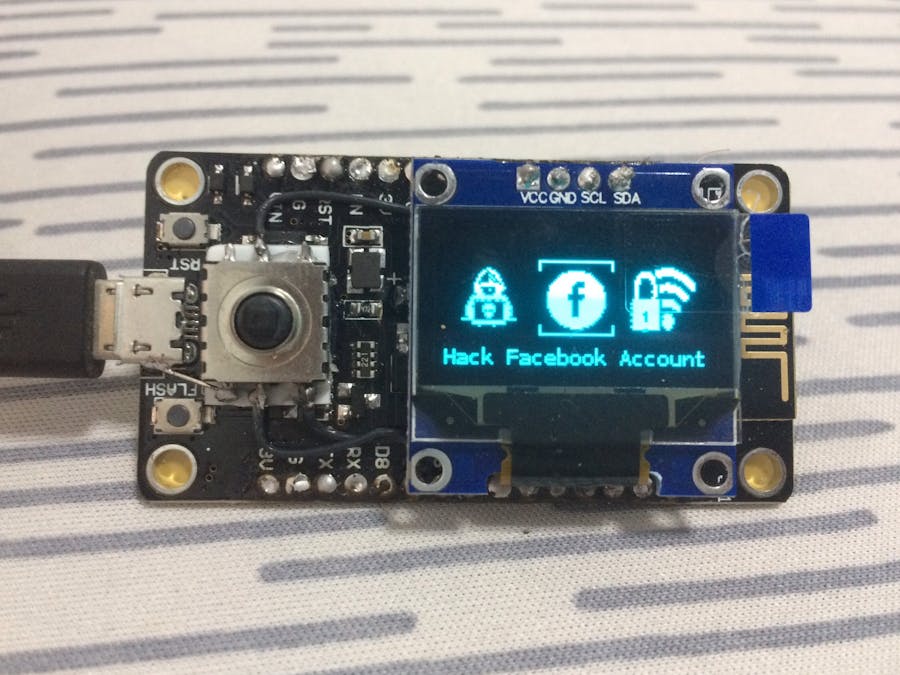
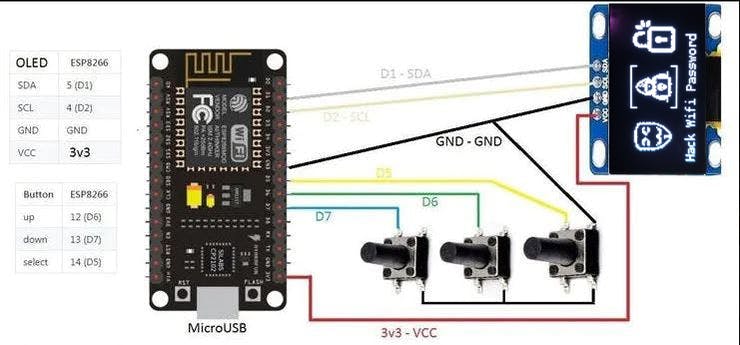
Read moreA super portable evil device, based on the ESP8266 board.
- Wi-Fi deauthentication attack: Scan for WiFi devices, block selected connections.
- Captive Portal: it creates a "free hotspot" and redirects the users to a registration page, where they - hopefully - enter their usual facebook/password combination. Anyway, it never makes them sign in
- Evil Twin: it looks for nearby protected networks and lets you select the target one, then it sets up an open access point with the same ESSID of the victim and it uses a captive portal to redirect the users to a page which requires the WiFi password "in order to complete the firmware upgrade".
- Beacon Spammer: it spams multiple WiFi beacons to make appear many fake access points on the nearby devices.
Disclaimer
- Usage of Wifiphisher for attacking infrastructures without prior mutual consistency can be considered as an illegal activity. It is the final user's responsibility to obey all applicable local, state and federal laws. Authors assume no liability and are not responsible for any misuse or damage caused by this program.
All contributions are welcome! Code, documentation, graphics, or even design suggestions are welcome; use GitHub to its fullest. Submit pull requests, contribute tutorials -- whatever you have to offer, it'll be appreciated.
This source code is built on Deauther



Comments