Crazyradio is an open-source 2.4GHz radio dongle originally intended for communicating with Crazyflie. Being open-source, it is designed to be hacked and enhanced for its designed purpose, and modified for others.
There is one trick though. The way the Crazyradio USB bootloader is set up is not safe against bugged firmware. The bootloader is launched by the firmware, so if the firmware is bugged or damaged, launching the bootloader might become impossible.
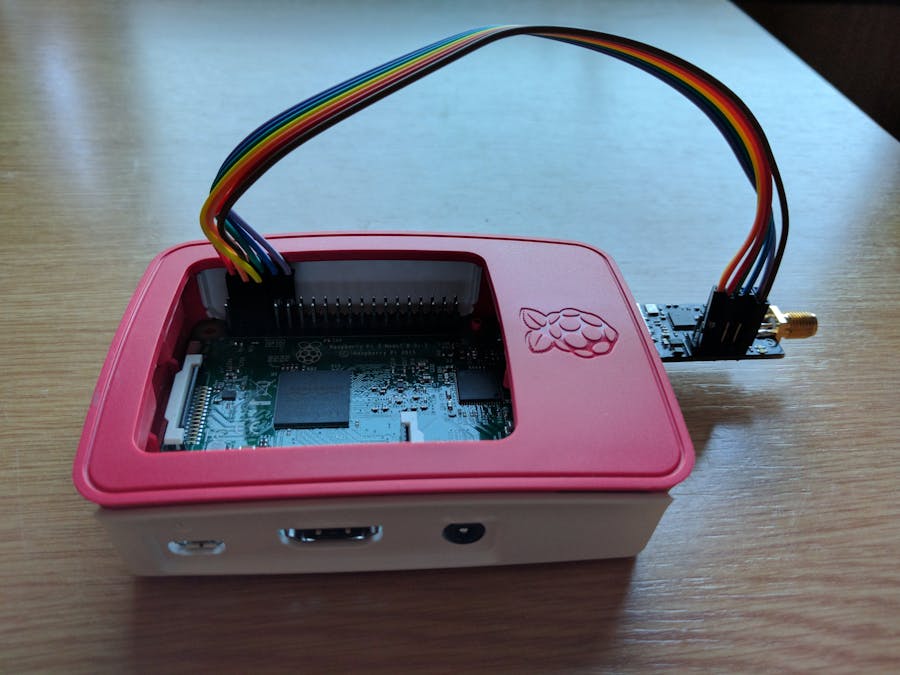
The solution is then to have an SPI programmer. This article describes how to use your Raspberry Pi as an SPI programmer to recover the USB bootloader. This allows it to work with the Crazyradio without the fear of locking it up.
Preparing your Raspberry PiThis has been tested on both Raspberry Pi 2 and 3. The pins used where present on all Raspberry Pis, including the first one, so it should work on Raspberry Pi 1 as well, but it has not been tested.
You need to run a recent version of Raspian (at least newer than December 2016). To clone the project, run the flashing script and the bootloader script. Some additional packages are needed. You can install them by running the following in a console:
$ sudo apt-get install git python-usb
The Crazyradio expansion port needs to be fitted with a 2x5 pin connector and connected to the Raspberry Pi expansion connector.
The default cabling is described at the beginning of the programming script:
# Script setup. Use this as a documentation to cable the Crazyradio or modify
# if you want to cable it differently.
# Name Pin on raspi Pin on Crazyradio
#-------------------------------------------
GND = 6 # 9
RESET = 3 # 3
PROG = 5 # 2
SCK = 7 # 4
MOSI = 8 # 6
MISO = 10 # 8
CS = 12 # 10
The pin number on both the Crazyradio and the Raspberry Pi correspond to the physical number on the connector.
The Crazyradio should be powered, either using the expansion port VDD pin (1) or by connecting it to a USB port. When using the Raspberry Pi connector the setup looks like this:
The script is located in the Crazyradio GitHub repos in the fix_bootloader folder. You will need to clone this repos in your Raspberry Pi and run the script. In a console:
$ git clone https://github.com/bitcraze/crazyradio-firmware
$ cd crazyradio-firmware/fix_bootloader
$ python fix_bootloader_raspi.py
Erasing page 0...
Writing 'JL 0x7800' instruction...
Flash content:
02
78
00
Fix written to flash. Disconnect the PROG wire, reconnect Crazyradio
and the bootloader should start!
If the flash content is displayed as 02 78 00, the Crazyradio should now boot the nordic bootloader!
Restarting the Crazyradio and flashing using the USB bootloaderWhen the script quits, all GPIOs are released and the PROG pin of the Crazyradio is kept in the prog position. This prevents the Crazyradio from booting the bootloader. So the first thing to do is to disconnect at least the prog pin (you can safely keep the other pin connected). When that is done the bootloader should start, you can verify it with dmesg and lsusb in a console:
$ dmesg
(...)
[ 340.240522] usb 1-1.5: new full-speed USB device number 6 using dwc_otg
[ 340.348743] usb 1-1.5: New USB device found, idVendor=1915, idProduct=0101
[ 340.348765] usb 1-1.5: New USB device strings: Mfr=1, Product=2, SerialNumber=0
[ 340.348778] usb 1-1.5: Product: nRF24LU1P-F32 BOOT LDR
[ 340.348790] usb 1-1.5: Manufacturer: Nordic Semiconductor
$ lsusb
Bus 001 Device 006: ID 1915:0101 Nordic Semiconductor ASA
Bus 001 Device 003: ID 0424:ec00 Standard Microsystems Corp. SMSC9512/9514 Fast Ethernet Adapter
Bus 001 Device 002: ID 0424:9514 Standard Microsystems Corp.
Bus 001 Device 001: ID 1d6b:0002 Linux Foundation 2.0 root hub
The nordic bootloader shows with both dmesg and lsusb. You can now flash a firmware. For example you can flash the latest release:
$ wget https://github.com/bitcraze/crazyradio-firmware/releases/download/0.53/
(...)
2017-04-20 10:51:48 (1.41 MB/s) - ‘cradio-pa-0.53.bin’ saved [5810/5810]
$ cd crazyradio-firmware/usbtools
$ sudo python nrfbootload.py flash ~/cradio-pa-0.53.bin
('Found nRF24LU1 bootloader version', '18.0')
Flashing:
Flashing 5810 bytes...
Flashing done!
Verifying:
Reading /home/pi/cradio-pa-0.53.bin...
Reading 5810 bytes from the flash...
Verification succeded!





Comments